Our Blogs
When Failure is Not an Option: Swissbit Storage Solutions for Mission-Critical Applications
In my latest blog post, I demonstrate once again how important data is in today's world. I also explain how Swissbit storage solutions secure data in different and demanding environments, including on land, in the air, at sea, and in space. Because: Swissbit storage...
The new iShield Key 2: Next-generation security key for phishing-resistant login and physical access
In my latest blog post, I unveil the iShield Key 2, a universal security key designed for both digital and physical access. I explain why the iShield Key 2 sets the global standard for hardware authentication and is the ideal phishing-resistant authentication solution...
How phishing resistant authentication can secure critical infrastructure from cyber threats
In my new blog post, I examine the critical infrastructure sector. This sector is becoming an increasingly common target of cyberattacks around the world. I will demonstrate how phishing-resistant authentication can effectively protect these facilities. Finally, I...
Introducing the Yubico Academy: Enabling partners for a phishing-resistant future
At Yubico, strong partnerships are fundamental to a more secure digital world. Our commitment goes beyond providing leading security keys; it’s about actively fostering the growth of our valued partners through impactful enablement programs. A cornerstone is...
CEO Corner: Maintaining stable growth while navigating global uncertainty
As we officially close out the first quarter of 2025, I am pleased we saw a quarter with solid growth and profitability along with ongoing demand for phishing-resistant authentication. We continue to see new types of high-profile cyber attacks appearing regularly,...
Cyber Resilience Act: Who is affected by CRA, and what needs to be done now
At the recent Embedded World trade fair in Nuremberg, it was one of the most discussed topics: the EU's Cyber Resilience Act (CRA). Many exhibitors and visitors seemed confused, as the law seems complex and its consequences unclear. It is therefore high time for a...
AI is booming — but proving you’re human matters more than ever
If you walked the show floor at the RSA Conference this year, you probably noticed the same thing I did: Artificial Intelligence (AI) is everywhere. Agentic AI. AI in threat detection. AI in firewalls. AI in identity management. AI-generated demos. AI everything. The...
Swissbit Storage Solutions for Data Centers, Enterprise and Edge Servers
The evolution of servers and data centers has fundamentally changed the way businesses operate. As efficiency and data processing capabilities increase, the need for reliable and robust data storage solutions is also growing. In my new article, I discuss the...
A unified physical and logical access management solution in one Security Key
In my first blog post, I will explore why it is advantageous for companies to consider physical and logical access management together. First, I will explain the difference, and then I will discuss the advantages of such a combined solution for companies. Finally, I...
Ditching passwords for good: Celebrating the inaugural World Passkey Day
Have you ever been stuck in a relationship with someone who constantly lets you down, exposes your secrets, and leaves you vulnerable? Odds are you cut your losses, packed up your things and moved on. Today is the day to do the same with your passwords: say goodbye...
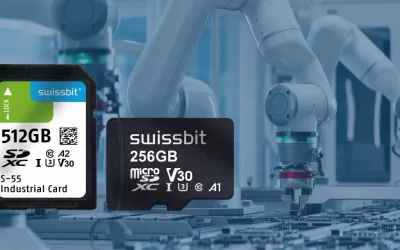
What makes Swissbit SD & microSD-Cards so special
In my first blog post, I provide a definitive analysis of the factors that enable certain SD and microSD cards to withstand harsh conditions. I explore the features that improve their durability, why Swissbit SD and microSD cards achieve the highest durability in...
Digital security’s unique role in protecting our environment
As sustainability expands to include social, economic, and technological challenges, cybersecurity has emerged as a top global threat – with cybercrime projected to cost $12 trillion this year. Stolen credentials and phishing account for 80% of breaches. At Yubico,...
Breaking down Australia’s plan to combat AI-driven phishing scams
Across Australia, cybercrime continues to be a major challenge impacting businesses, critical infrastructure and consumers alike. The use of AI by bad actors across the spectrum of cybercrime is on the rise, and as a result, credential phishing scams are becoming...
5 fast cybersecurity tips to clean up your digital life
With today being Identity Management Day, now is the perfect time to take stock of your online presence, update security settings, and ensure that your personal data remains protected from cyber threats like phishing. We’re also seeing increasing concerns of DeepSeek...
Bypassing MFA: The Rise of Adversary-in-the-Middle Attacks
An Adversary-in-the-Middle (AitM) phishing attack is an advanced form of credential theft in which attackers insert themselves between a user and a legitimate authentication service to intercept credentials and session tokens. This method allows attackers to bypass...
Think “good enough” is enough? Think again about mobile devices as authenticators
Presented by David Treece, VP Solutions Architecture, Yubico & Erik Parkkonen, Sr. Solutions Architect, Yubico About this talk As your organization navigates Microsoft’s MFA mandate and other recent MFA mandates to improve your organization's security posture,...
Navigating the PCI DSS 4.0 transition and meeting compliance with phishing-resistant YubiKeys
In just a few days, on March 31, 2025, decision makers in industries that involve payment processing – including financial services, retail & hospitality and telecommunications – are tasked to finalize the transition to Payment Card Industry Data Security Standard...
Swissbit Storage for Industrial Automation and Robotics
Industrial automation and robotics have fundamentally changed production. While efficiency and productivity are increasing, the requirements for reliable and robust data storage are also growing. In my new article, I show the challenges that companies have to overcome...
One Key, Many Doors
Businesses need to protect access to restricted areas just as they need to protect access to endpoint devices and sensitive internal data. State of the art token solutions meet both requirements at the same time, saving time and money. Two developments are...
Building cyber resilience with Yubico and Microsoft
In today’s digital landscape, cyber threats are evolving at an unprecedented pace: every second, a phishing attack takes place. In fact, over 80% of these attacks are the result of stolen login credentials and almost 70% of phishing attacks relied on AI last year...
What companies should consider when it comes to the cyber security of embedded systems
In my latest blog post, I focus on the cyber security of embedded systems and the associated special requirements. In addition, there are the risks arising from the increasing networking of embedded systems. Finally, I present solutions that improve the security of...
Six requirements for Edge Server products and their fulfillment by Swissbit
In my new blog post, I delved into the topic of edge servers and explored the unique demands they place on storage solutions. By identifying six critical requirements, I was able to assess how Swissbit’s product portfolio aligns with the needs of edge computing. The...
Yubico’s commitment to innovation: Phishing-resistance as a cornerstone for cyber resilience
As phishing attacks have reached an unprecedented level of frequency and sophistication, enterprises must prioritize authentication that is phishing-resistant – regardless of the business scenario, platform or device users are working with. This is why Yubico...
Cybersecurity: EU regulations that companies should know now
In my new blog post, I highlight the importance of the current EU regulations for companies. I emphasize that companies not only need to be aware of NIS2, RED, CRA and Data Act, but also need to take proactive measures to comply with these regulations and meet their...
CEO Corner: Wrapping up a strong year, and looking ahead to 2025 and beyond
It’s no secret that 2024 was a big year of growth for Yubico, highlighted across many notable achievements by our team and increasing demand from our customers. As discussed in my previous post, following a transformative year driven by key cybersecurity trends like...
Swissbit Storage for Network and Communications
My new article focuses on the network and telecommunications industry (NetCom). These companies around the world depend on their critical data being stored securely, accessibly, and reliably often under the most demanding conditions. My article outlines solutions and...
The rise of AI-driven phishing attacks: What to know and how to be secure
As businesses continue learning the benefits that artificial intelligence (AI) assisted computing tools provide, we’re continuing to see rapid interest and adoption of the technology – especially within the enterprise. Most conversations up until recently have...
Advantages of NVMe Features for Industrial Storage
In my first blog post I provide a comprehensive overview of Non-Volatile Memory Express (NVMe), emphasizing its significance and the advantages it offers. Additionally, I outline which NVMe features are supported by Swissbit storage products, offering valuable...
Technology Authentication 101: Passkeys for Enterprises?
In my new blog post, I take a closer look at the development of FIDO Passkeys. Technology giants such as Microsoft, Google and Apple are pushing the topic of passwordless authentication on the consumer side. And on the corporate side? The Foundation of FIDO and...
Works with YubiKey Spotlight: Expanded partnerships redefining phishing-resistance in 2025
2024 was an exciting year for Yubico and our partners. Together, we achieved remarkable milestones, launching innovative solutions and forging stronger partnerships – all aimed at delivering the most impactful cybersecurity solutions and user experience for our...